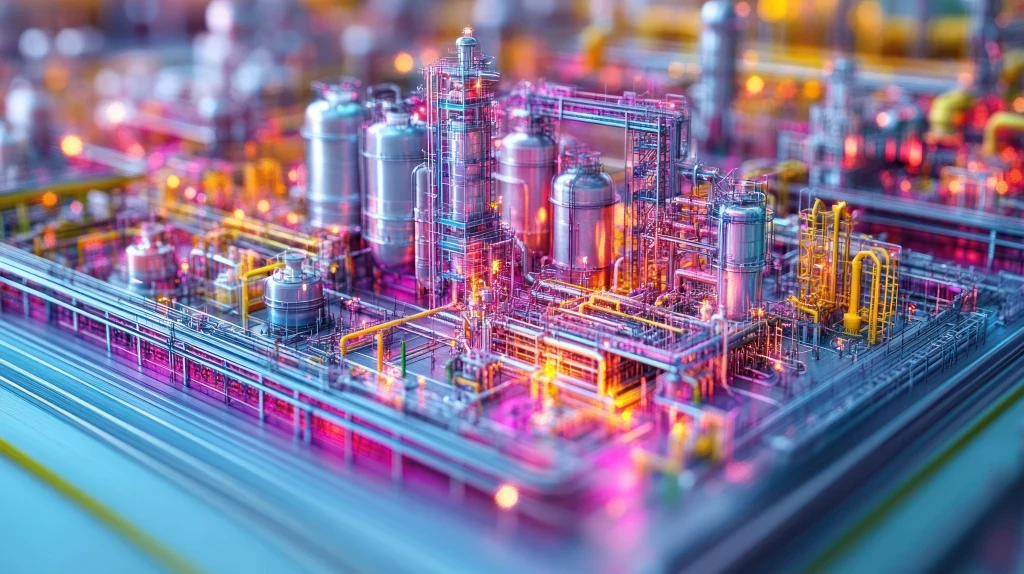
Cyber Security in the Oil & Gas Industry - Keeping Systems and Data Safe
Add bookmarkThe oil and gas industry has a unique set of risks. Unlike most other sectors where protecting Intellectual Property (IP) takes a prominent role within the corporate risk management framework, the dangers associated with oil and gas places the security of people and the environment at the forefront of their risk policies.
The white paper looks at this intellectual property paradox; the challenge of determining how to best keep IP safe, yet accessible to those who need it. The universal trend of cyber-attacks, understanding the threat landscape, and how connecting IT and operational technology (OT) has changed this threat landscape.
This white paper explores how security could learn from safety within the oil and gas industry, how security should be reporting on near incidents as well as actual incidents, and how to incorporate people, process and technology in a best-practice approach to security.
In this white paper you will:
|
1 Learn how the oil and gas industry can translate their disciplined approach to health, safety and the environment (HSE) to cyber security. 2 Find out how an integrated and intelligent approach to energy industry cyber security can help your organisation move towards a more stringent application of cyber security. 3 Learn more about intellectual property paradox and understand the threat landscape. 4 See how companies can adapt to have a successful cyber security programme. |
This white paper is for you if you work in the fields of:
- IT security
- Network security
- Application infrastructure management
- SCADA/ICS/DCS
- Process control